Flowblade 2.24.1
Bugfix release.
Bugfix release.
lazbuild - (c9c6be0).exe extension!!! - (35d2ebd).deb - (e95aca8)Package variable - (13c55ce)v4 of git-cliff-action - (81d613b)build-* - (16a54a5)tx-push recipe - (d293d64).ini files on run-* - (c513e53)run-gtk2, run-qt5 - (04650d9)tx-push to Makefile - (3ceed39)secrets.mk - (123a2e7)Note
For a list of all the changes up to date, please read CHANGELOG.md.
Bump version for v12.17 release
Release created in https://github.com/OpenRCT2/OpenRCT2/actions/runs/24303301342
SHA256 checksums:
545aacbbce6e0f00097c6a2efe9d1d7a4226f20f8f120304e41324e955406387 ./OpenRCT2-v0.5.0-Linux-bookworm-x86_64.tar.gz
b390cba3ecfecb5c3188fe33b8391a7045a039739c382e0fa6b9ff0f0d4c101e ./OpenRCT2-v0.5.0-windows-symbols-arm64.zip
7736205ec96e93203c129038475026764a267d7883f11095b4ed0b98ca49852c ./OpenRCT2-v0.5.0-macos-universal.zip
af94d53b5259c28d8639f264e8dfe88a4ca68aa60b90631cb27a66caa895a6b2 ./OpenRCT2-v0.5.0-sha256sums.txt
f714431d73d77e66f4808e728a4b54c14c59b931b36d49e4d4ac238e2490aac3 ./OpenRCT2-v0.5.0-windows-symbols-win32.zip
8d1d6fd2afe324ed8b74b4483ee5693256cdc69a1a3159818bbbba49914b2e13 ./OpenRCT2-v0.5.0-windows-installer-x64.exe
20260b77324bd8e9cad95a8e4da2ef69d56a95e6715de0a64d824be8e57333b5 ./OpenRCT2-v0.5.0-Linux-trixie-x86_64.tar.gz
99d626e6aca3168ff48900dc4c3aa0c3f3a7026f5974181840b62f1f099202b1 ./OpenRCT2-v0.5.0-windows-symbols-x64.zip
5557043fe8e12457307a1bdf743a1daeb772bba9c36637664731fdebed19b948 ./OpenRCT2-v0.5.0-windows-portable-x64.zip
74d1b920033ee54effb35674fa53659ad8b942378649a98dd7efc6ba923f236c ./OpenRCT2-v0.5.0-windows-installer-win32.exe
e1dbdf337c3a02a03b7722752a749303277c20fcae962471705f214d4c14b9fc ./OpenRCT2-v0.5.0-Linux-resolute-x86_64.tar.gz
8f5660356449a086667d02525fc63c9d85e9883f47cb50d501febc4476551d41 ./OpenRCT2-v0.5.0-windows-installer-arm64.exe
cb174ca94e48a3aa8d83fa8f9e5b13df281b8d56f1bd67f7a5f5ed5dc0addb31 ./OpenRCT2-v0.5.0-android.apk
0d1f01be35d8d4632aa3dc67d33b084f610576a2b1d966011964951eac15e303 ./OpenRCT2-v0.5.0-windows-portable-win32.zip
e1c27003ba27bea8dc7cf7c1f41fc51e2a271269b8911ffa19905dc2447a3d97 ./OpenRCT2-v0.5.0-windows-portable-arm64.zip
42885a0f51bed6f145488161a6d932912050a15f2f3ac32bb7a5d48d42b03a6d ./OpenRCT2-v0.5.0-Linux-noble-x86_64.tar.gz
780c2a48f0ab917dd4b10079eb13c57093919410a5c7a356492c728315b6cb9a ./OpenRCT2-v0.5.0-linux-x86_64.AppImage
Thank you for your donations:
One-time
Monthly
SESSION_SECRET_FILE and OAUTH_CLIENT_SECRET_FILE environment variable supportonAvatarResolve plugin hookname.full (#179)name.components in vCard parser
Thank you for your donations:
One-time
Monthly
The Asterisk Development Team would like to announce
the release of asterisk-23.3.0.
The release artifacts are available for immediate download at
https://github.com/asterisk/asterisk/releases/tag/23.3.0
and
https://downloads.asterisk.org/pub/telephony/asterisk
Repository: https://github.com/asterisk/asterisk
Tag: 23.3.0
This release resolves issues reported by the community
and would have not been possible without your participation.
Thank You!
The Asterisk Development Team would like to announce
the release of asterisk-22.9.0.
The release artifacts are available for immediate download at
https://github.com/asterisk/asterisk/releases/tag/22.9.0
and
https://downloads.asterisk.org/pub/telephony/asterisk
Repository: https://github.com/asterisk/asterisk
Tag: 22.9.0
This release resolves issues reported by the community
and would have not been possible without your participation.
Thank You!
The Asterisk Development Team would like to announce
the release of asterisk-20.19.0.
The release artifacts are available for immediate download at
https://github.com/asterisk/asterisk/releases/tag/20.19.0
and
https://downloads.asterisk.org/pub/telephony/asterisk
Repository: https://github.com/asterisk/asterisk
Tag: 20.19.0
This release resolves issues reported by the community
and would have not been possible without your participation.
Thank You!
/status.php (#9470)Full Changelog: v4.0.0-beta.471...v4.0.0-beta.472
Full Changelog: v4.0.0-beta.470...v4.0.0-beta.471
The Extended Stable channel has been updated to 146.0.7680.188 for Windows and Mac which will roll out over the coming days/weeks.
The Chrome team is delighted to announce the promotion of Chrome 147 to the stable channel for Windows, Mac and Linux. This will roll out over the coming days/weeks.
Security Fixes and Rewards
Note: Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.
This update includes multiple security fixes. Please see the Chrome Security Page for more information.
[$43000][493319454] Critical CVE-2026-5858: Heap buffer overflow in WebML. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-17
[$43000][494158331] Critical CVE-2026-5859: Integer overflow in WebML. Reported by Anonymous on 2026-03-19
[$11000][486495143] High CVE-2026-5860: Use after free in WebRTC. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-02-22
[$3000][486927780] High CVE-2026-5861: Use after free in V8. Reported by 5shain on 2026-02-23
[TBD][470566252] High CVE-2026-5862: Inappropriate implementation in V8. Reported by Google on 2025-12-21
[TBD][484527367] High CVE-2026-5863: Inappropriate implementation in V8. Reported by Google on 2026-02-14
[TBD][490642831] High CVE-2026-5864: Heap buffer overflow in WebAudio. Reported by Syn4pse on 2026-03-08
[TBD][491884710] High CVE-2026-5865: Type Confusion in V8. Reported by Project WhatForLunch (@pjwhatforlunch) on 2026-03-12
[TBD][492218537] High CVE-2026-5866: Use after free in Media. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-13
[TBD][492668885] High CVE-2026-5867: Heap buffer overflow in WebML. Reported by Syn4pse on 2026-03-14
[TBD][493256564] High CVE-2026-5868: Heap buffer overflow in ANGLE. Reported by cinzinga on 2026-03-16
[TBD][493708165] High CVE-2026-5869: Heap buffer overflow in WebML. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-18
[TBD][495534710] High CVE-2026-5870: Integer overflow in Skia. Reported by Google on 2026-03-23
[TBD][495679730] High CVE-2026-5871: Type Confusion in V8. Reported by Google on 2026-03-24
[TBD][496281816] High CVE-2026-5872: Use after free in Blink. Reported by Google on 2026-03-25
[TBD][496301615] High CVE-2026-5873: Out of bounds read and write in V8. Reported by Google on 2026-03-25
[$11000][485397279] Medium CVE-2026-5874: Use after free in PrivateAI. Reported by Krace on 2026-02-18
[$4000][430198264] Medium CVE-2026-5875: Policy bypass in Blink. Reported by Lyra Rebane (rebane2001) on 2025-07-08
[$2000][41485206] Medium CVE-2026-5876: Side-channel information leakage in Navigation. Reported by Lyra Rebane (rebane2001) on 2023-12-18
[TBD][333024273] Medium CVE-2026-5877: Use after free in Navigation. Reported by Cassidy Kim(@cassidy6564) on 2024-04-05
[TBD][365089001] Medium CVE-2026-5878: Incorrect security UI in Blink. Reported by Shaheen Fazim on 2024-09-06
[TBD][40073848] Medium CVE-2026-5879: Insufficient validation of untrusted input in ANGLE. Reported by parkminchan, working for SSD Labs Korea on 2023-10-01
[TBD][424995036] Medium CVE-2026-5880: Incorrect security UI in browser UI. Reported by Anonymous on 2025-06-14
[TBD][454162508] Medium CVE-2026-5881: Policy bypass in LocalNetworkAccess. Reported by asnine on 2025-10-22
[TBD][480993682] Medium CVE-2026-5882: Incorrect security UI in Fullscreen. Reported by Anonymous on 2026-02-02
[TBD][482958590] Medium CVE-2026-5883: Use after free in Media. Reported by sherkito on 2026-02-09
[TBD][484547633] Medium CVE-2026-5884: Insufficient validation of untrusted input in Media. Reported by xmzyshypnc on 2026-02-15
[TBD][485203823] Medium CVE-2026-5885: Insufficient validation of untrusted input in WebML. Reported by Bryan Bernhart on 2026-02-17
[TBD][485397283] Medium CVE-2026-5886: Out of bounds read in WebAudio. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-02-18
[TBD][486079015] Medium CVE-2026-5887: Insufficient validation of untrusted input in Downloads. Reported by daffainfo on 2026-02-20
[TBD][486506202] Medium CVE-2026-5888: Uninitialized Use in WebCodecs. Reported by Identified by the Octane Security Team: Giovanni Vignone, Paolo Gentry, Robert van Eijk on 2026-02-22
[TBD][486906037] Medium CVE-2026-5889: Cryptographic Flaw in PDFium. Reported by mlafon on 2026-02-23
[TBD][487259772] Medium CVE-2026-5890: Race in WebCodecs. Reported by Casper Woudenberg on 2026-02-24
[TBD][487471101] Medium CVE-2026-5891: Insufficient policy enforcement in browser UI. Reported by Tianyi Hu on 2026-02-25
[TBD][487568011] Medium CVE-2026-5892: Insufficient policy enforcement in PWAs. Reported by Tianyi Hu on 2026-02-25
[TBD][487768771] Medium CVE-2026-5893: Race in V8. Reported by QYmag1c on 2026-02-26
[$1000][481882038] Low CVE-2026-5894: Inappropriate implementation in PDF. Reported by Povcfe of Tencent Security Xuanwu Lab on 2026-02-05
[TBD][374285495] Low CVE-2026-5895: Incorrect security UI in Omnibox. Reported by Renwa Hiwa @RenwaX23 on 2024-10-18
[TBD][40064543] Low CVE-2026-5896: Policy bypass in Audio. Reported by Luan Herrera (@lbherrera_) on 2023-05-13
[TBD][419921726] Low CVE-2026-5897: Incorrect security UI in Downloads. Reported by Farras Givari on 2025-05-24
[TBD][470295118] Low CVE-2026-5898: Incorrect security UI in Omnibox. Reported by saidinahikam032 on 2025-12-19
[TBD][474817168] Low CVE-2026-5899: Incorrect security UI in History Navigation. Reported by Islam Rzayev on 2026-01-11
[TBD][475265304] Low CVE-2026-5900: Policy bypass in Downloads. Reported by Luan Herrera (@lbherrera_) on 2026-01-13
[TBD][479673903] Low CVE-2026-5901: Policy bypass in DevTools. Reported by Povcfe of Tencent Security Xuanwu Lab on 2026-01-29
[TBD][483109205] Low CVE-2026-5902: Race in Media. Reported by Luke Francis on 2026-02-10
[TBD][483771899] Low CVE-2026-5903: Policy bypass in IFrameSandbox. Reported by @Ciarands on 2026-02-11
[TBD][483851888] Low CVE-2026-5904: Use after free in V8. Reported by Zhenpeng (Leo) Lin at depthfirst on 2026-02-12
[TBD][483899628] Low CVE-2026-5905: Incorrect security UI in Permissions. Reported by daffainfo on 2026-02-12
[TBD][484082189] Low CVE-2026-5906: Incorrect security UI in Omnibox. Reported by mohamedhesham9173 on 2026-02-13
[TBD][484665123] Low CVE-2026-5907: Insufficient data validation in Media. Reported by Luke Francis on 2026-02-15
[TBD][485115554] Low CVE-2026-5908: Integer overflow in Media. Reported by Ameen Basha M K & Mohammed Yasar B on 2026-02-17
[TBD][485203821] Low CVE-2026-5909: Integer overflow in Media. Reported by Mohammed Yasar B & Ameen Basha M K on 2026-02-17
[TBD][485212874] Low CVE-2026-5910: Integer overflow in Media. Reported by Ameen Basha M K & Mohammed Yasar B on 2026-02-17
[TBD][485785246] Low CVE-2026-5911: Policy bypass in ServiceWorkers. Reported by lebr0nli of National Yang Ming Chiao Tung University, Dept. of CS, Security and Systems Lab on 2026-02-19
[TBD][486498791] Low CVE-2026-5912: Integer overflow in WebRTC. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-02-22
[TBD][487195286] Low CVE-2026-5913: Out of bounds read in Blink. Reported by Vitaly Simonovich on 2026-02-24
[TBD][490023239] Low CVE-2026-5914: Type Confusion in CSS. Reported by Syn4pse on 2026-03-05
[TBD][494341335] Low CVE-2026-5915: Insufficient validation of untrusted input in WebML. Reported by ningxin.hu@intel.com on 2026-03-20
[TBD][490139441] Low CVE-2026-5918: Inappropriate implementation in Navigation. Reported by Google on 2026-03-05
[TBD][483423893] Low CVE-2026-5919: Insufficient validation of untrusted input in WebSockets. Reported by Richard Belisle on 2026-02-10
We would also like to thank all security researchers that worked with us during the development cycle to prevent security bugs from ever reaching the stable channel.
Many of our security bugs are detected using AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, or AFL.
Interested in switching release channels? Find out how here. If you find a new issue, please let us know by filing a bug. The community help forum is also a great place to reach out for help or learn about common issues.
Srinivas Sista
Google Chrome
nginx-1.29.8 mainline version has been released.
Various security fixes.
Fixed an issue where certain parts of web pages, such as drop-down menus and specific styles, did not appear correctly when printing. (Bug 2026109)
Fixed an issue where some website error pages displayed generic connection messages instead of the specific error code and description provided by the server. (Bug 2023800)
Fixed a crash that occurred when using certain security keys or WebAuthn features for two-factor authentication. (Bug 2026688)
Fixed an issue on Linux where the browser toolbar could become unresponsive to mouse clicks after dragging a tab when using Wayland. (Bug 2022238)
Fixed a layout issue where text inside certain graphics (SVG) appeared shifted or misaligned from its intended position. (Bug 2024647)
Fixed an issue where the "Send to device" option failed to work when used from the Open Tabs section in Firefox View. (Bug 2023201)
Introduced a new enterprise policy that allows administrators to directly manage and control AI-related features within Firefox. (Bug 2019983)
Fixed an issue where enterprise policies for the browser homepage and start page were not being applied correctly. (Bug 2027888)
Introduced a new enterprise policy that allows administrators to prevent the built-in VPN and IP protection features from being available to users. (Bug 2022365)
Reference link to 149.0 release notes.

The latest version of AppCenter comes with some more improvements to the updates view including now showing all ongoing app installations, upgrades, and removals. Plus the “Last checked” information is now always shown in the “Up to Date” apps header. And we fixed an issue where in-app notifications were sent for every update installed.
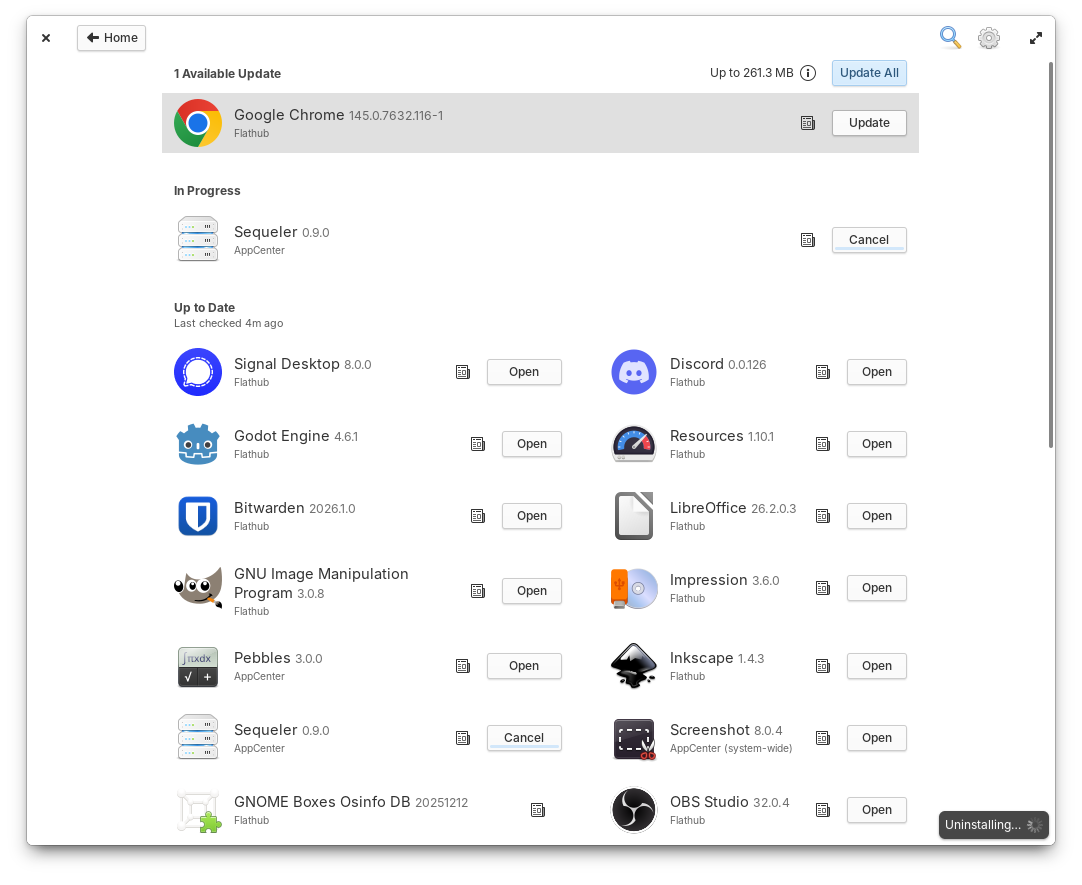
AppCenter now shows ongoing operations in the updates view
There’s also some more performance improvements including much faster startup times, faster info fetching for apps that can be installed from multiple stores, and quite a bit of code simplification and cleanup, thanks to Leonhard.
The latest version of Code comes with a number of fixes and a couple new tricks. In the Project’s sidebar, sorting project folders is now a toggle-able setting rather than a one-time action, the Terminal pane now follows the currently selected project’s path, and Jeremy fixed an issue that could cause the number of results for a global search to be incorrect. Plus, Loric fixed an issue that could cause a crash on startup or during certain global searches, and added a new setting to disable syntax highlighting for a more distraction-free editing experience. The High Contrast style has improved contrast for line numbers, thanks to the help of Micah. And it’s no longer possible to open multiple PasteBin dialogs thanks to Calle.
We recently removed System Settings as a default dock item—since it’s accessible from several other places and dock space is at a premium—but, there were some expressed concerns about discoverability. So we’ve added some additional information to the final page of Onboarding to close the gap. This page shows even after selecting “Skip All”, so folks are always shown how to access additional System Settings and set up their computer how they like it.
Onboarding now explains ways to access System Settings
We now also support a new accent color option thanks to Ryo: the smooth and creamy “Latte”. This is a great new option for big fans of soft neutrals and can be selected both during Onboarding and from Desktop Settings. And, Desktop settings now supports long-press secondary-click on touch screens for removing wallpapers.
Font settings have also been expanded to allow an open-ended selection. So whether you need a font like OpenDyslexic for accessibility reasons, feel more productive with a coding font like Fira, or just want to have a bit of fun, you now have to option to customize text to your liking.
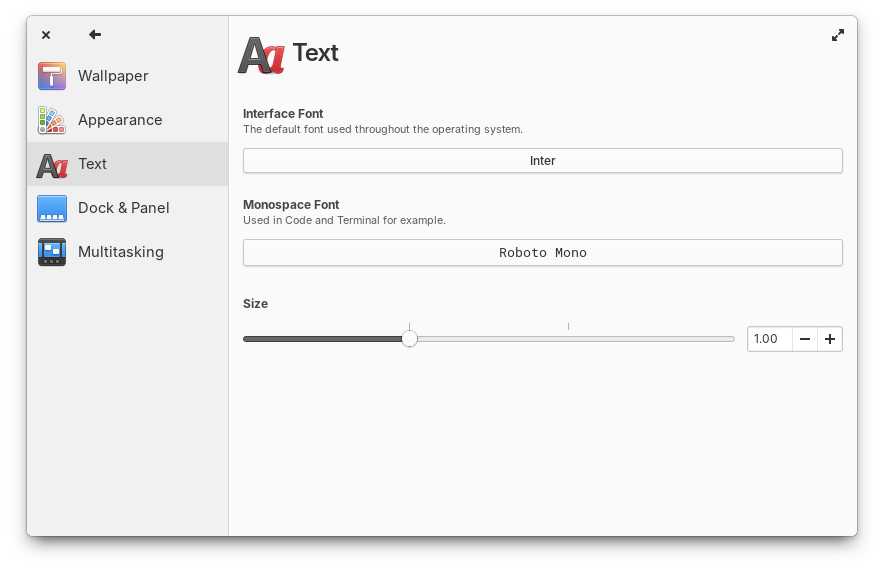
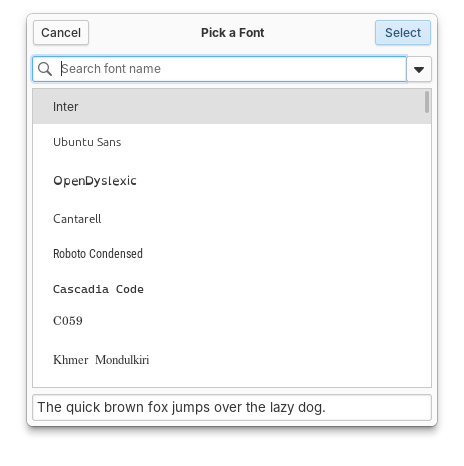
Text settings now includes an open ended font selection dialog
In keyboard settings, Ryo also addressed an issue that would cause IBus to send a notification in Secure sessions, and Leo added support for using the “Tools” key present on some keyboards in custom keyboard shortcuts.
And of course we’ve got some more window manager improvements including performance improvements while zooming and a fix for an issue that would cause workspaces to change during pinch gestures by Leo. And Leonhard fixed issues with fullscreen Firefox videos, flickering when the Reduce Motion setting was enabled, and an issue where the correct window for apps with multiple windows would sometimes not be focused when selected from the Dock.
As always, pop open System Settings → System on elementary OS 8 and hit “Update All” to get these updates plus your regular security, bug fix, and translation updates. Or set up automatic updates and get a notification when updates are ready to install!
Quite a lot has been happening lately to prepare for OS 9 but I think it deserves its own blog post, so hang tight! For now, I’ll say that we’re getting close to a place where we might have bootable daily builds and we’re making good progress on some big projects like a new design for Portals, improved CJK input support and a new on-screen keyboard, a GTK4 powered panel, our next-generation app framework and visual design and more!
At the moment we’re at 20% of our monthly funding goal and 287 Sponsors on GitHub! Shoutouts to everyone helping us reach our goals here. Your monthly sponsorship funds development and makes sure we have the resources we need to give you the best version of elementary OS we can!
Monthly release candidate builds and daily Early Access builds are available to GitHub Sponsors from any tier! Beware that Early Access builds are not considered stable and you will encounter fresh issues when you run them. We’d really appreciate reporting any problems you encounter with the Feedback app or directly on GitHub.
lodash, samlify and @xmldom/xmldom dependencies and add defu override (#27033 by @br41nslug)@directus/app@15.8.0@directus/api@35.0.2@directus/composables@11.3.0create-directus-extension@11.0.34@directus/errors@2.3.1@directus/extensions-registry@3.0.24@directus/extensions-sdk@17.1.2@directus/memory@3.1.7@directus/validation@2.0.22